Unbiased picks • US B2B • Updated
Best Identity & Access Management (IAM) Software ()
Best identity access management software: comparison & rankings
This guide compares the best identity and access management software for US B2B teams, based on real-world use cases, security depth, and operational fit. It’s decision-focused: pick the IAM that fits your governance needs (SSO, lifecycle, policies, conditional access) — not a generic security checklist.
Want the fastest answer? Start with the comparison table below.
Quick verdict: top picks ()
Okta
Strong IAM default for SSO + policies + lifecycle needs in SaaS-first environments.
Microsoft Entra ID
Best fit if your org already runs on Microsoft (Azure + M365) and needs conditional access governance.
JumpCloud
Good pick when you need directory + SSO + device/IT ops alignment under one admin workflow.
Ping Identity
Strong option for complex enterprise identity patterns and federated access governance.
No affiliate links are active at this time. Rankings are editorial.
For most SaaS-first US B2B teams, Okta is the safest all-around IAM choice in .
Rankings are editorial. We do not accept paid placements.
Jump to a short review
How we pick winners
US-only, B2B scope
This comparison is built for US-based B2B teams (SMB → mid-market → enterprise) evaluating identity and access management software. We focus on governance realities: onboarding/offboarding, policy control, and access consistency.
What qualifies as IAM
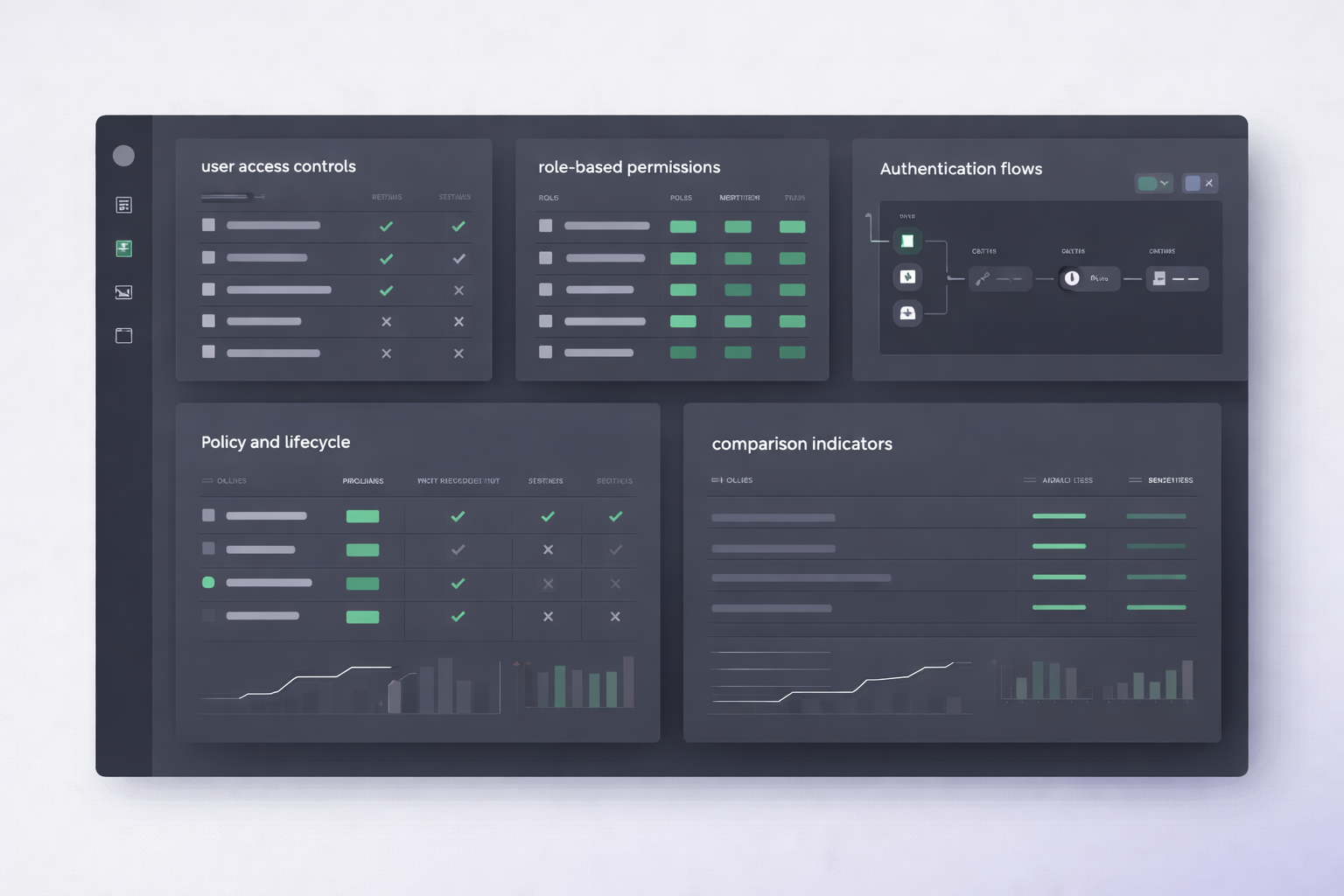
We only rank tools that function as a true IAM platform (not password managers, not MFA-only apps, not network/Zero Trust suites). A tool must cover multiple identity pillars (directory, SSO, authn/authz, lifecycle, conditional access).
What is IAM? Identity & Access Management (IAM) is how organizations control who can access what, under which conditions, across apps and devices — with governance that scales (policies, roles, lifecycle, and audit readiness).
Compare the best IAM tools ()
Use this table to shortlist identity and access management software and quickly pick the right IAM platform for your organization.
| Software | Best for | Price (from) |
Standout strengths | Score | |
|---|---|---|---|---|---|
|
Okta |
SaaS-first IAM governance | Varies by plan |
• Strong SSO + policy control • Mature admin patterns • Broad integrations |
8.9 | Check price |
|
Microsoft Entra ID |
Microsoft 365 / Azure orgs | Varies by plan |
• Conditional access alignment • Microsoft ecosystem fit • Centralized identity control |
8.7 | Check price |
|
JumpCloud |
SMB / mid-market IT ops | Varies by plan |
• Directory + SSO workflows • Good admin ergonomics • Fits IT ops patterns |
8.4 | Check price |
|
Ping Identity |
Enterprise federation & complexity | Varies by plan |
• Enterprise identity patterns • Federation-focused workflows • Governance-oriented tooling |
8.3 | Check price |
|
OneLogin |
SSO-first access standardization | Varies by plan |
• SSO standardization • Policy + access management • Good for IT-led rollouts |
8.1 | Check price |
|
Google Cloud Identity |
Google Workspace organizations | Varies by plan |
• Google-first identity fit • Centralized user management • Works with Workspace governance |
8.0 | Check price |
Pricing changes frequently and depends on plan, billing terms, and enterprise packaging. Always verify on the vendor’s site.
👉 Want the simplest IAM decision? Okta is our safe pick for most SaaS-first B2B teams.
Our top pick (deep dive): Okta
Okta is our top pick and a safe default identity and access management software choice when your goal is consistent access governance across many SaaS apps. It’s usually the lowest-risk IAM option for organizations that need SSO, policy control, and scalable administration.
- Strong access governance patterns (policies + admin workflows)
- Reliable SSO standardization across many apps
- Fits SaaS-first, multi-app environments
- Pricing/packaging depends on enterprise needs
- May be unnecessary if you are fully suite-locked (Microsoft/Google)
- Companies managing many SaaS tools and user roles
- Security/IT teams needing scalable identity governance
- Organizations prioritizing policy consistency
- Very small teams with minimal access governance needs
- Organizations using only Microsoft or only Google with no multi-app complexity
- Teams looking for password managers (separate category)
Short reviews (money-focused)
Below are short, decision-focused notes to help you choose identity and access management software fast, based on real-world governance needs.
Okta — Best overall for most SaaS-first teams
Best if you need IAM governance at scale: SSO standardization plus policy-driven access control.
- Strong SSO and identity governance patterns
- Good fit for multi-app SaaS environments
- Mature admin workflows for IT/security teams
- Pricing depends on packaging and enterprise needs
- Can be unnecessary for suite-only environments
Microsoft Entra ID — Best for Microsoft 365 / Azure organizations
Best if your identity stack is Microsoft-first and you want policy-driven access control aligned with that ecosystem.
- Strong fit inside Microsoft ecosystems
- Conditional access governance patterns
- Centralized identity control for Microsoft-first orgs
- Packaging depends on Microsoft licensing
- Less attractive if you are not Microsoft-first
JumpCloud — Best for SMB + IT ops alignment
Best if you want directory + access control plus admin workflows that match day-to-day IT operations.
- Strong “IT ops + identity” workflow fit
- Good admin ergonomics for small/mid teams
- Practical approach for standardizing access
- Best fit depends on org size and requirements
- Enterprise needs may push toward other IAM stacks
Ping Identity — Best for enterprise federation patterns
Best if you operate complex identity environments and need federation-oriented governance at scale.
- Strong enterprise identity patterns
- Federation-focused workflows
- Designed for large org governance needs
- May be overkill for small teams
- Packaging depends on enterprise requirements
OneLogin — Good for SSO standardization and access control
Best if your priority is standardizing SSO and access policies in a structured IT rollout.
- Solid SSO standardization patterns
- Access control and admin workflows
- Good fit for IT-led implementations
- Fit depends on your lifecycle/governance requirements
- Enterprise packaging varies by needs
Google Cloud Identity — Best for Google Workspace organizations
Best if you run Google Workspace and want centralized identity management aligned with that ecosystem.
- Google-first ecosystem fit
- Centralized user management
- Works well with Workspace governance patterns
- May be less ideal in Microsoft-first environments
- Enterprise governance fit depends on requirements
What to look for (fast IAM decision checklist)
When comparing identity and access management software, focus on governance needs — not buzzwords or feature checklists.
- SSO coverage: can you standardize login across your core apps?
- Policies & authorization: roles, RBAC, and access rules that match teams and risk.
- Conditional access: device trust / context-based controls when needed.
- Identity lifecycle: onboarding/offboarding and role changes without manual chaos.
- Directory + source of truth: a centralized directory that scales with growth.
- Governance fit: audit readiness and policy consistency (without overengineering).
Note: password managers and MFA-only tools are different categories and are not ranked on this IAM page.
How we evaluate IAM software
To rank IAM platforms, we focus on whether a product can support enterprise-grade identity governance at scale — not isolated features or marketing claims.
What we consider
- Lifecycle coverage: how well identity changes are governed over time
- Access controls: roles/policies that stay manageable as orgs grow
- Authentication fit: SSO + strong auth controls as part of a broader IAM model
- Identity foundation: directory + identity sources handled cleanly
- Context awareness: conditional controls where applicable to the platform
- Operational fit: admin workflow without daily governance friction
How rankings stay editorial
- We rank only tools that qualify as IAM platforms (not partial categories).
- We consider multiple dimensions and compare tools by real-world fit (not feature count).
- We use vendor documentation for factual checks (pricing/packaging can change).
- Exact weighting and scoring formulas are internal and not disclosed.
Who this guide is for (and not for)
- SMBs and mid-market teams needing scalable identity governance
- IT / security teams standardizing access across multiple SaaS apps
- Organizations adopting conditional access and policy control
- Companies that want consistent onboarding/offboarding workflows
- Individuals looking for password managers (separate category)
- MFA-only app comparisons (separate category)
- Zero Trust / SASE platform shopping (can be mentioned, not ranked here)
- Teams that only need a single login for one app
FAQ
What is IAM (Identity & Access Management)?
Identity and access management software helps control who can access what across your apps and systems — including SSO, identity lifecycle, roles/policies, and conditional access.
What’s the best IAM software for most B2B teams?
For most SaaS-first organizations, Okta is a strong default because it focuses on scalable identity governance. If you’re Microsoft-first, Microsoft Entra ID can be the more natural fit.
Is a password manager an IAM tool?
Not in this guide. Password managers store credentials for individuals/teams, but they are not full IAM platforms. They are evaluated on separate pages to avoid category overlap.
Should Zero Trust tools be ranked on an IAM page?
No. Network/Zero Trust suites can interact with identity, but they are not ranked as IAM platforms here. They may be mentioned where relevant, without being positioned as IAM winners.
Bottom line
This guide ranks identity and access management software (not password managers, not MFA-only tools) based on governance, policy control, and operational fit for US B2B teams.
Safest all-around pick: Okta.
Microsoft-first orgs: Microsoft Entra ID.
SMB + IT ops workflows: JumpCloud.
Enterprise federation patterns: Ping Identity.
SSO standardization: OneLogin.
Google Workspace orgs: Google Cloud Identity.
Bottom line: choose IAM based on governance needs (lifecycle + policies + conditional access) — not feature volume.
Rankings are editorial and reflect our analysis of identity and access management software. No affiliate links are active at this time.
Sources: Okta, Microsoft Entra, JumpCloud, OneLogin, Ping Identity, Google Cloud Identity